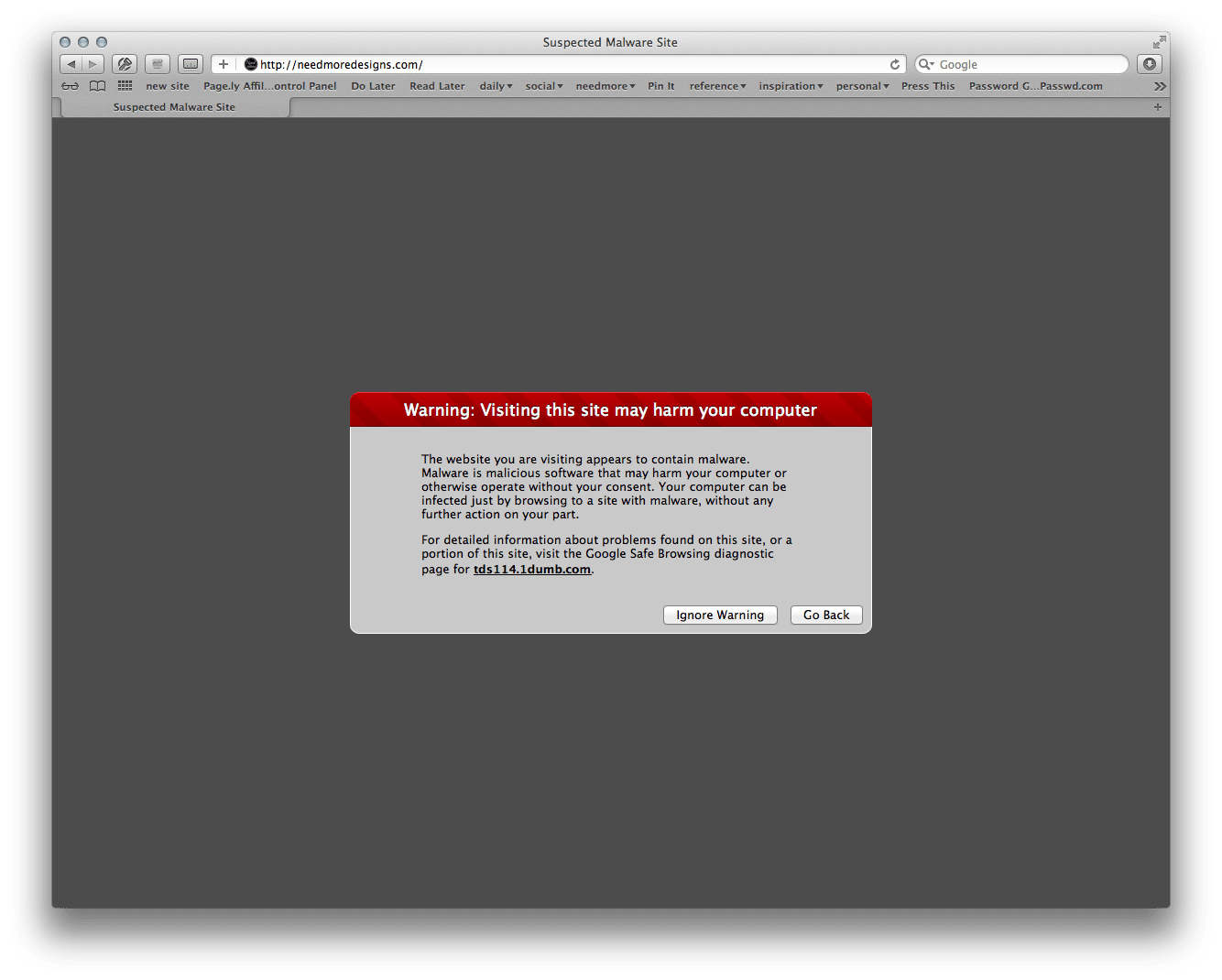
A week ago, we walked into what can only be described as every website owner’s worst nightmare, the dreaded malware warning. Warning: Visiting this site may harm your computer! How could we have gotten to this point?
We have had a website for over 8 years now without such an incident occurring. Then, a couple weeks ago, we made the decision to move the Needmore website to fancy, fully hosted hosting package at WP Engine. (We were seduced by claim of lightening fast, secure hosting.) Their motto is: The buck stops with us and we take that responsibility very seriously. These are big words, but unfortunately not at all what we experienced when our website was hacked.
Feb 13th
- The day starts like any other day, with Raymond in the studio at the crack of dawn. At 7:20 am, he notices and alerts WP Engine that our website is displaying the above malware notification.
- At 8:41 am, we further submit a screenshot as proof of the issue so that WP Engine will begin taking care of the issue.
- 10:24 am, after some back and forth, our site is finally submitted to their security team (over three hours from when we first alerted them to the issue). We still feel confident as they claim that sites are, on average, back up and running within 4 hours. Theoretically, with only one more hour to go, we are in the home stretch.
- At 1:28 pm, we begin to feel slightly nervous since we haven’t heard a thing from WP Engine. We write.
- At 1:30 pm, our contact at WP Engine says they have fixed our website completely and resubmitted it to Google. We are relieved for all of five minutes. Then, we discover that they have broken our website so that, now, only code mumbo jumbo shows up. (This is not a good thing to submit to Google as proof of a fix.)
- At 1:45 pm, fearing Google will see the broken and send us into infinite search engine purgatory, we write WP Engine and ask them to quickly restore a functioning website.
…silence…
- Finally, at 5 pm, we call and get someone to restore the website right then and there. Alas, it is too late.
- At 6:30 pm, Google lets us know that they have failed our website on the updated malware scan. (Google say that the site hasn’t actually been fixed and supply us with exact pages and code as proof.) We let WP Engine know. Again, they say they are working on it. We also notice that the FTP access to our site has changed, without us knowing, and so we cannot grab the site ourselves to move it elsewhere. We also ask for the updated information.
…silence…
February 14th
- At 7:40 am, a full 24 hours after WP Engine has started “working on it”, our site is still showing the malware notice and now all Google searches come up with a warning. Our site is no longer viewable or findable. We write WP Engine once again. Still, nothing.
- At 10:45 am, we call and talk to someone at WP Engine. We explain the situation in detail and politely ask them to make restoring the website a priority. They suggest that they will be willing to “send another email” about the issue to their security team.
- We eventually get the new FTP access. And so, at 11 am, we pull our site off of the WP Engine server, fix it up, put it on our former hosting plan, and resubmit to Google.
- At 11:33 am, WP Engine writes to us, suggesting that we point our site back to their servers. Fat chance.
We made the right move pulling our website. By the end of the day, Google approved our site again and began allowing visitors. By the morning of the 15th, all warnings were removed from search engines and our website doesn’t appear to have suffered any loss of ranking.
This situation reminds us of the importance of proper and sincere communication. It is a fact of life online: websites do get hacked. (Not often, in the grander scheme of things, but it does happen.) There were no obvious issues with our website that would have suggested an easy prey; our passwords were secure and our plug-ins and WordPress version were up-to-date. It would be easy to point to the new host as the culprit. However, it could still have been a fluke that ours was hacked only after we switched to WP Engine. We’ll never know.
Regardless of why the site was hacked, our experience post-incident was extremely frustration. It is entirely possible that the WP Engine team was furiously working on restoring our website for the 24+ hours it was compromised. Unfortunately, if they were, it wasn’t presented to us as such. Instead, we only knew that emails had been sent or someone had been alerted. Had anyone, at any time, given us the the impression that our situation was a priority, we would have felt much more at ease. Instead, we were forced to take a strong lead role in nudging them along on the most basic of tasks. And, in the end, we had to pull our site and fix the situation ourselves. This all could have been avoided by good communication from WP Engine.
Finally, as we attempted to have our account canceled, they actually showed their first sincere interest in how we felt as customers: “We would be very interested to know why you would like to cancel. Was there something that we could have improved in order for you to stay with us?”
Oh dear.